If you enjoy our newsletter, please consider to be a paid subscriber to help us keep more news and updates coming out.
Highlights
GeminiJack.PostQuantum Encryption + AI.AI Secure by Design.Google secures agentic browsing.10,000+ Docker images leak secrets.
Deep Dive
GeminiJack Noma Security
Targeted Google Gemini Enterprise.
Exploits indirect prompt injection.
Malicious prompts hide in files.
AI forced to leak data.
Google resolved this specific issue.
Similar attacks are likely on others.
Specialized security layers required.
Shadow IT increases risk.
Future breaches could be unrecoverable.
PostQuantum Encryption + AI SecurityBoulevard
Quantum computers break encryption.
Attackers can poison training data.
Model inversion steals sensitive secrets.
Adversarial inputs trick AI.
Behavioral analysis detects anomalies.
Monitor latency and variance.
Implement post-quantum security frameworks.
Adopt post-quantum cryptography immediately.
AI Secure by Design PaloAlto Networks
Adoption outpaces security measures.
Legacy tools miss AI threats.
Attacks manipulate AI’s probabilistic logic.
The government mandates secure AI design.
New roadmap bridges policy gap.
Must secure agents and infrastructure.
Purpose-built strategies replace retrofitting.
Security instills trust in AI.
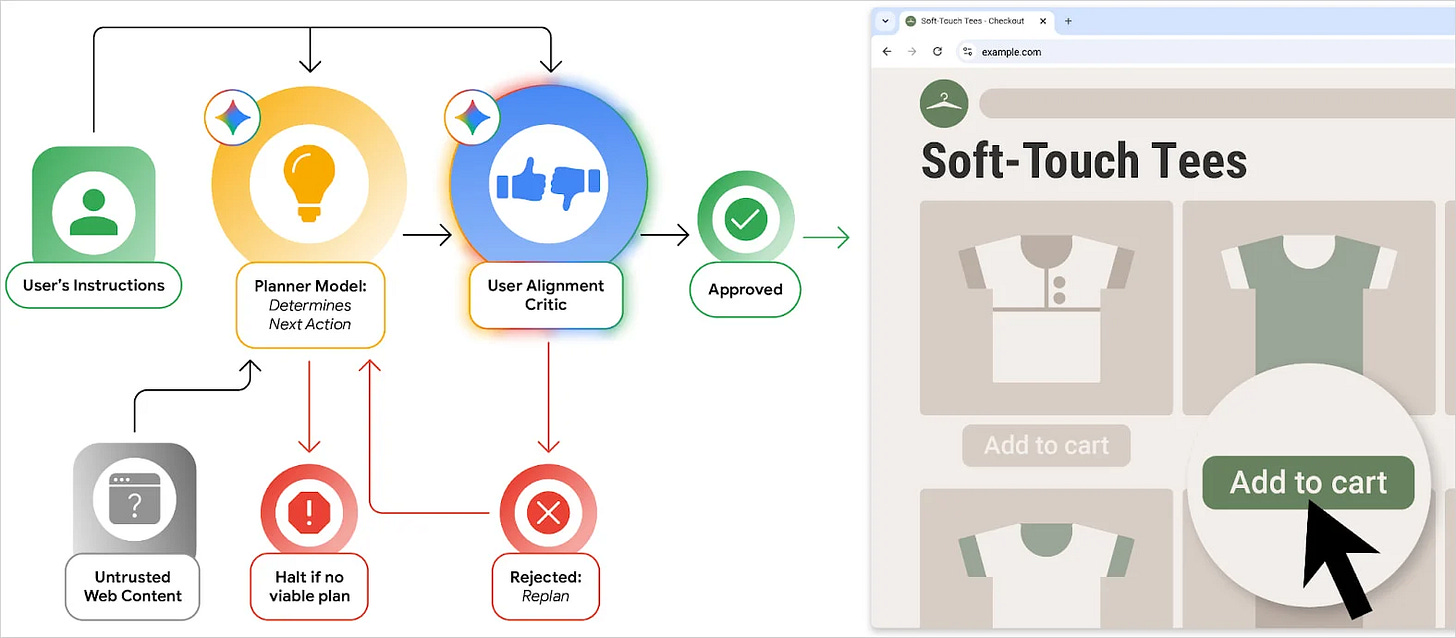
Google secures agentic browsing BleepingComputer
“User Alignment Critic” vets actions.
The secondary model prevents prompt injection.
Origin Sets restrict data access.
Sensitive tasks require user approval.
Real-time scanning blocks malicious prompts.
Automated red-teaming tests defenses.
$20,000 bounty for security researchers.
10,000+ Docker images leak secrets TheRegister
Fortune 500s and banks exposed.
AI tokens are frequent leaks.
Shadow IT bypasses corporate security.
Personal accounts host enterprise secrets.
Deleted files don’t revoke keys.
75% of keys remain active.
Automated scanners harvest exposed keys.


![[Free ebook] Agentic AI & Quantum](https://substackcdn.com/image/fetch/$s_!N9hN!,w_140,h_140,c_fill,f_auto,q_auto:good,fl_progressive:steep,g_auto/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F9efd87d8-2c87-450b-8ca7-e028c7996cab_908x908.heic)

![[Available] Book Report Q3, 2025](https://substackcdn.com/image/fetch/$s_!HI5v!,w_140,h_140,c_fill,f_auto,q_auto:good,fl_progressive:steep,g_auto/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F62b0655a-9a73-4382-8201-d9007269e7ad_900x900.jpeg)