AWS Graviton4: Native encryption on cloud.
History, signifiance, performance, security consideration and implication
tl;dr We follow the story of last week about Apple Intelligence pushed back by questions for Personal Cloud Computing with tracking prompts and similar to Google Android hybrid approach. We ask a deeper question related about the state of the art of native encrypted cloud to examine how we are ready by this week’s launch of Graviton4.
Amazon Web Services' (AWS) introduction of the Graviton4 processor, while offering compelling performance and efficiency benefits, necessitates a careful evaluation from a security perspective. This report provides insights and actionable recommendations for CISOs to effectively assess and mitigate potential risks associated with adopting Graviton4-based cloud infrastructure.
HISTORY & SIGNIFICANCE
From Mobile to the Cloud: A Legacy of Efficiency
Graviton's journey began with a simple concept: bring the power efficiency of mobile Arm chips to the data center. While others had tried and failed, AWS Annapurna Labs succeeded, launching the first Graviton in 2018. Each generation has brought significant improvements, and Graviton4 is no exception.
"Graviton" refers to a family of server processors designed by Amazon Web Services (AWS). These processors are custom-built by AWS and are based on the Arm architecture, unlike the more common x86 architecture used in most servers today (from companies like Intel and AMD).
Why is Graviton a big deal?
Efficiency: Arm's architecture generally uses less power than x86, leading to lower electricity costs for AWS and potentially lower prices for customers that fits to company's goal towards ESG, security and budgets.
Performance: While not universally better for all tasks, Graviton excels in workloads common to cloud computing, like running web applications, handling databases, and data processing.
Competition: It challenges the dominance of Intel and AMD in the server market, potentially leading to more innovation and better options for everyone.
Technical Specifications:
Key Features:
Neoverse V2 Cores: Graviton4 utilizes Arm's powerful and efficient Neoverse V2 cores, which feature enhancements for cloud workloads, including improved single-threaded performance and enhanced vector processing capabilities.
Increased Core Count: With up to 96 cores per socket and support for dual-socket configurations, Graviton4 provides a significant boost in compute density, allowing for consolidation of workloads and reduced infrastructure costs.
DDR5 Memory: The adoption of DDR5 memory technology delivers higher bandwidth and increased memory capacity, essential for demanding applications like in-memory databases and data-intensive analytics.
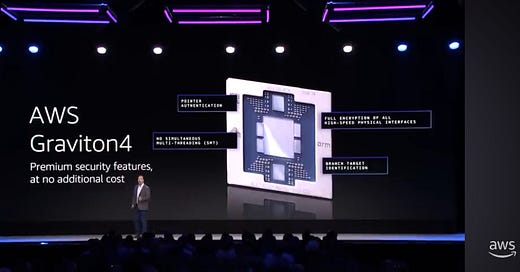
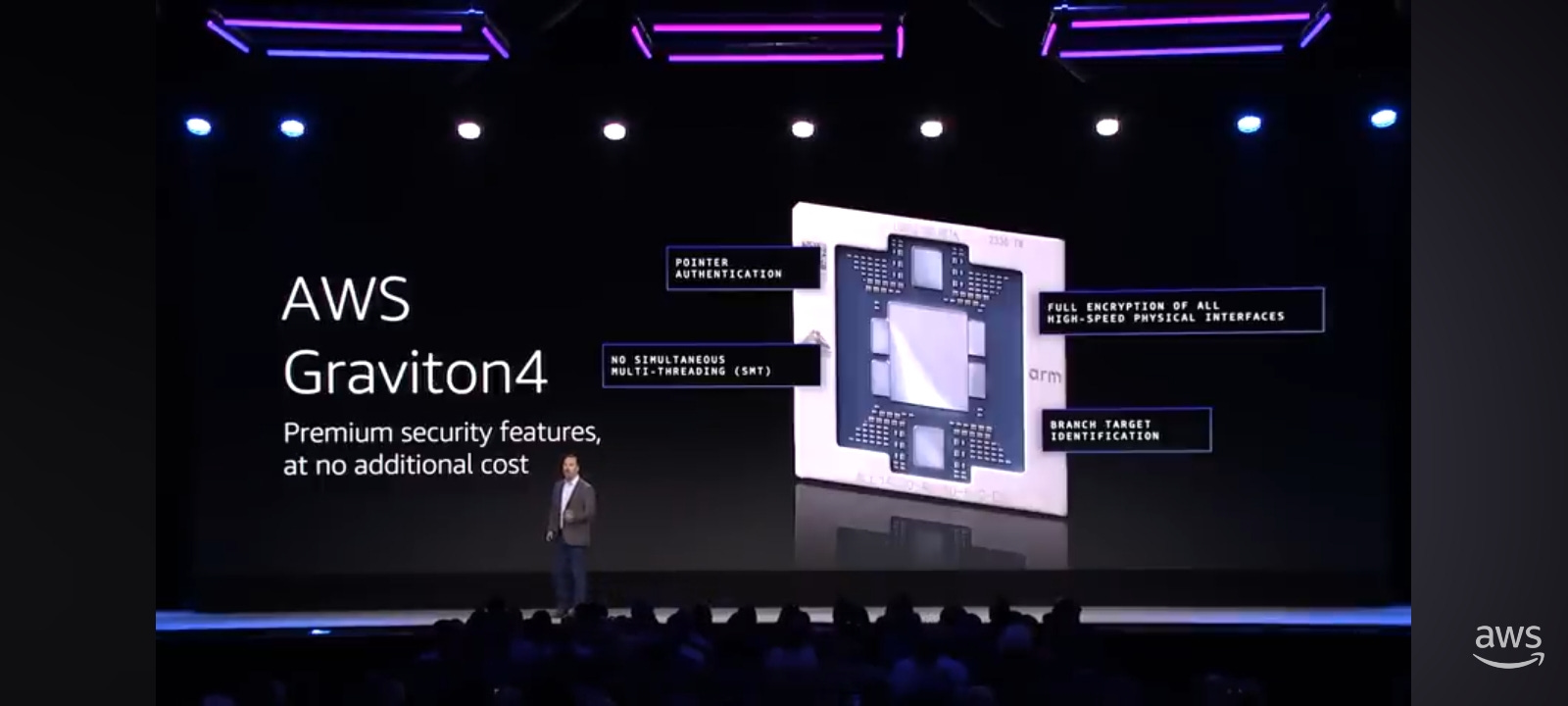
Enhanced Security: Graviton4 incorporates hardware-level security features such as encrypted high-speed interfaces and Branch Target Identification (BTI) to mitigate vulnerabilities and protect sensitive data.
Compelling security advantages
Customizable Architecture: Security From the Ground Up
Reduced Attack Surface: Arm, the architecture behind Graviton, is known for its RISC (Reduced Instruction Set Computing) design. This generally means a smaller and simpler instruction set compared to x86, potentially reducing the attack surface that vulnerabilities could exploit.
AWS Control: Since AWS designs Graviton in-house, they have greater control over the entire hardware stack, from the silicon to the hypervisor. This allows for tighter integration of security features and potentially faster patching of vulnerabilities.
Hardware-Enabled Security Features:
Encrypted Interfaces: Graviton4 specifically mentions "encrypted high-speed hardware interfaces." This likely refers to on-chip encryption for data moving between different components of the processor or even between the processor and memory. This is crucial for protecting data in use and in transit within the server itself.
Branch Target Identification (BTI): Graviton4 also incorporates BTI, a security feature designed to mitigate against specific types of control-flow hijacking attacks (common exploits used in data breaches).
Pointer Authentication: While not explicitly mentioned in the CSV, Arm's architecture supports Pointer Authentication, a hardware-level mechanism to prevent attackers from manipulating pointers in memory, a common attack vector.
"Clean Slate" Advantage & Future Potential:
Legacy Baggage: x86 architecture, due to its long history, carries legacy baggage (older design decisions, backwards compatibility needs) that can sometimes introduce security risks. Arm, being relatively newer in the server space, can incorporate modern security best practices from the start.
Rapid Innovation: The rapid development cycle of the Graviton family allows AWS to incorporate emerging security technologies and countermeasures more quickly, keeping pace with evolving threats.
Isolation and Trust in the Cloud:
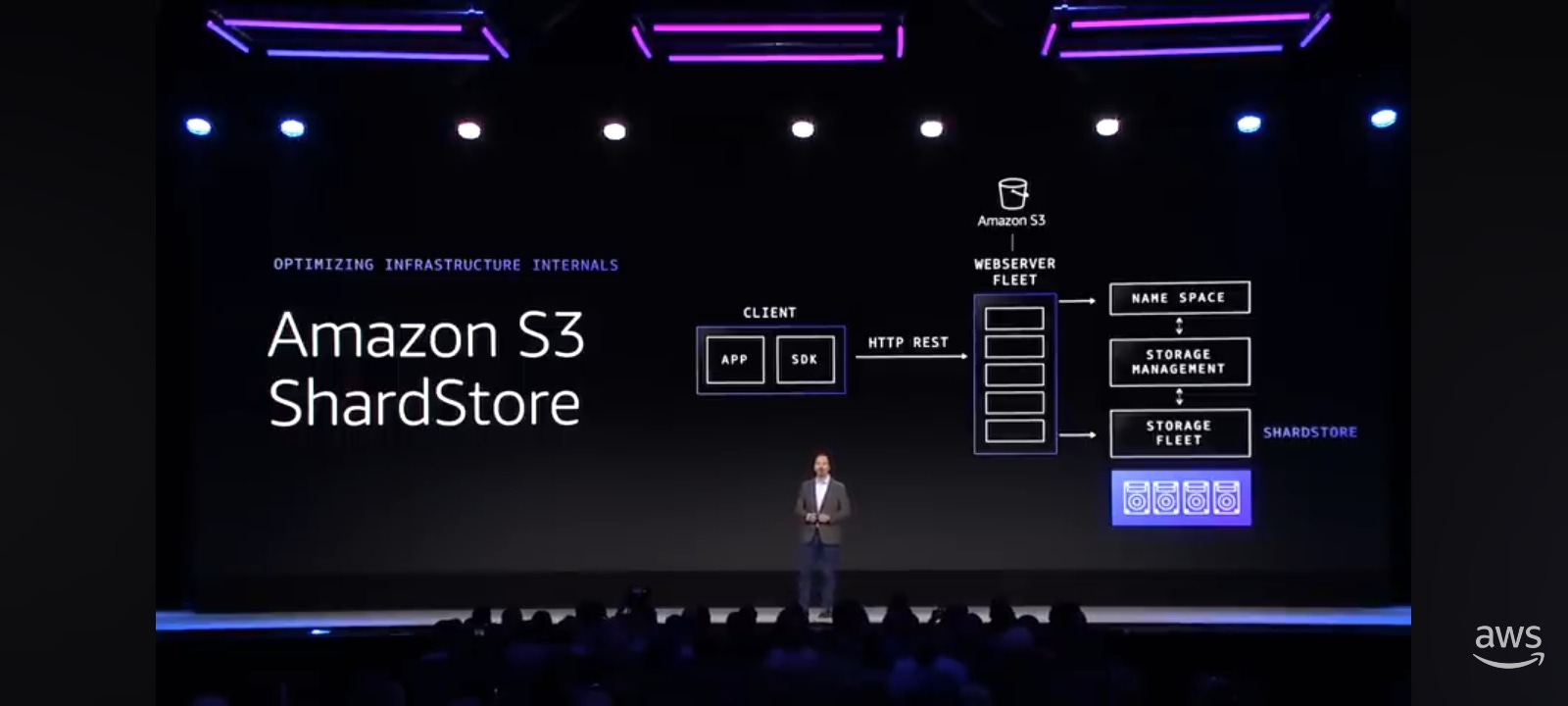
Nitro System: AWS already utilizes its Nitro System, a combination of dedicated hardware and lightweight hypervisors, to provide isolation between customer instances and the underlying infrastructure. Graviton, with its security features, strengthens this isolation further.
Root of Trust: A potential future direction is to leverage Graviton's on-chip security features to establish a more robust root of trust for cloud workloads. This could enhance secure boot processes and make it significantly harder for attackers to tamper with the most fundamental levels of the system.
THE PERFORMANCE & PRICE
Graviton4's power stems from its sophisticated technical design:
Arm Neoverse V2 Cores: These cores represent a significant leap over previous Arm architectures, specifically designed for cloud workloads. Graviton4 leverages these cores' enhanced single-threaded performance and robust vector processing capabilities.
Massive Core Count: With up to 96 cores per socket and dual-socket configurations reaching 192 cores, Graviton4 delivers exceptional compute density. This allows for consolidation of workloads onto fewer servers, directly translating to cost savings.
DDR5 Memory: A Speed Boost: The adoption of DDR5 memory technology is crucial. It provides the bandwidth and capacity necessary for handling data-intensive tasks like in-memory databases and real-time analytics, where speed is paramount.
Security by Design: Recognizing the critical importance of security in the cloud, AWS has integrated features like encrypted high-speed interfaces and Branch Target Identification (BTI) directly into the Graviton4 silicon. This hardware-level approach strengthens defenses against a range of vulnerabilities.
The Need for Speed: A Performance Leap Backed by Numbers
AWS Graviton4, built on the Arm Neoverse V2 platform, is engineered for demanding cloud workloads. But raw specs only tell part of the story. Let’s examine the data:
Database Dominance: Benchmarks reveal Graviton4 delivers up to 40% higher performance for database applications compared to comparable x86-based instances. This translates to faster query processing, smoother transactions, and ultimately, improved user experiences for data-driven applications.
Web Applications Get a Boost: In a world obsessed with speed, web applications on Graviton4 are up to 30% faster. This means quicker page loads, more responsive interfaces, and a competitive edge in a digital landscape where every millisecond counts.
Java Powerhouse: For enterprises relying on Java applications, Graviton4 shines with up to 45% faster performance. This translates into faster code execution, improved scalability, and potentially significant cost savings on compute resources.
The Efficiency Equation: Turning Savings into Profits
AWS offers Graviton4 processors on its R8g EC2 instances. Pricing varies depending on instance size, region, and purchase options (on-demand, reserved instances, etc.). Generally, AWS positions Graviton4-based instances as offering better price-performance compared to equivalent x86-based instances.
Graviton4's efficiency goes beyond mere marketing speak. It's a core design principle translating into tangible economic benefits:
Lower Energy Consumption: Built on the energy-efficient Arm architecture, Graviton4 consumes significantly less power than comparable x86 processors, directly impacting operational costs for data centers.
Increased Compute Density: Higher core counts and optimized architecture enable greater workload consolidation, requiring fewer servers to handle the same amount of work, further reducing infrastructure costs.
Applications:
Graviton4 excels in a wide range of applications, including:
Databases: High core count and fast memory make it ideal for running demanding database workloads, including relational databases like MySQL and PostgreSQL and in-memory databases like Redis.
Web Applications: Improved single-threaded performance and optimized software stacks contribute to faster response times and enhanced user experiences for web applications.
Microservices: Graviton4's efficiency and scalability make it well-suited for running containerized microservices architectures.
High-Performance Computing (HPC): While not specifically designed for HPC, Graviton4's vector processing capabilities can accelerate certain HPC workloads.
Security implication and considerations
Potential Advantages:
Reduced Attack Surface: Graviton's Arm architecture, characterized by its RISC design, inherently presents a smaller attack surface compared to traditional x86 architectures. This could potentially reduce the number of exploitable vulnerabilities.
Enhanced Control and Transparency: AWS's end-to-end control over Graviton's design and implementation provides a greater degree of transparency into the hardware and firmware, potentially allowing for more robust security assessments and faster patching of vulnerabilities.
Hardware-Enabled Security Features: Graviton4 incorporates hardware-level security features such as encrypted interfaces and Branch Target Identification (BTI) that can enhance data protection and mitigate certain types of attacks.
Potential Challenges:
Evolving Threat Landscape: The relative novelty of Arm in the server space means that the threat landscape is still evolving. Attackers are constantly seeking new vulnerabilities, and Graviton4-specific exploits may emerge over time.
Software Ecosystem Maturity: While the software ecosystem for Arm is growing rapidly, it's not yet as mature as that of x86. This could lead to potential compatibility challenges with existing security tools or a smaller pool of security expertise.
Legacy Security Tooling Compatibility: Existing security tools and processes may need to be reassessed for compatibility with Arm-based environments. This includes vulnerability scanners, security information and event management (SIEM) systems, and intrusion detection/prevention systems.
In the next week, we will try to examine new security tech stack of AWS introduced this year to have a comprehensive view of what is going thoroughfully.