In this blog, I am trying to make a quick update of a landscape Y2 - GenAI explosion. This is also a following part of the first post as my learning experience in this emergent field.
The first iPhone trojan
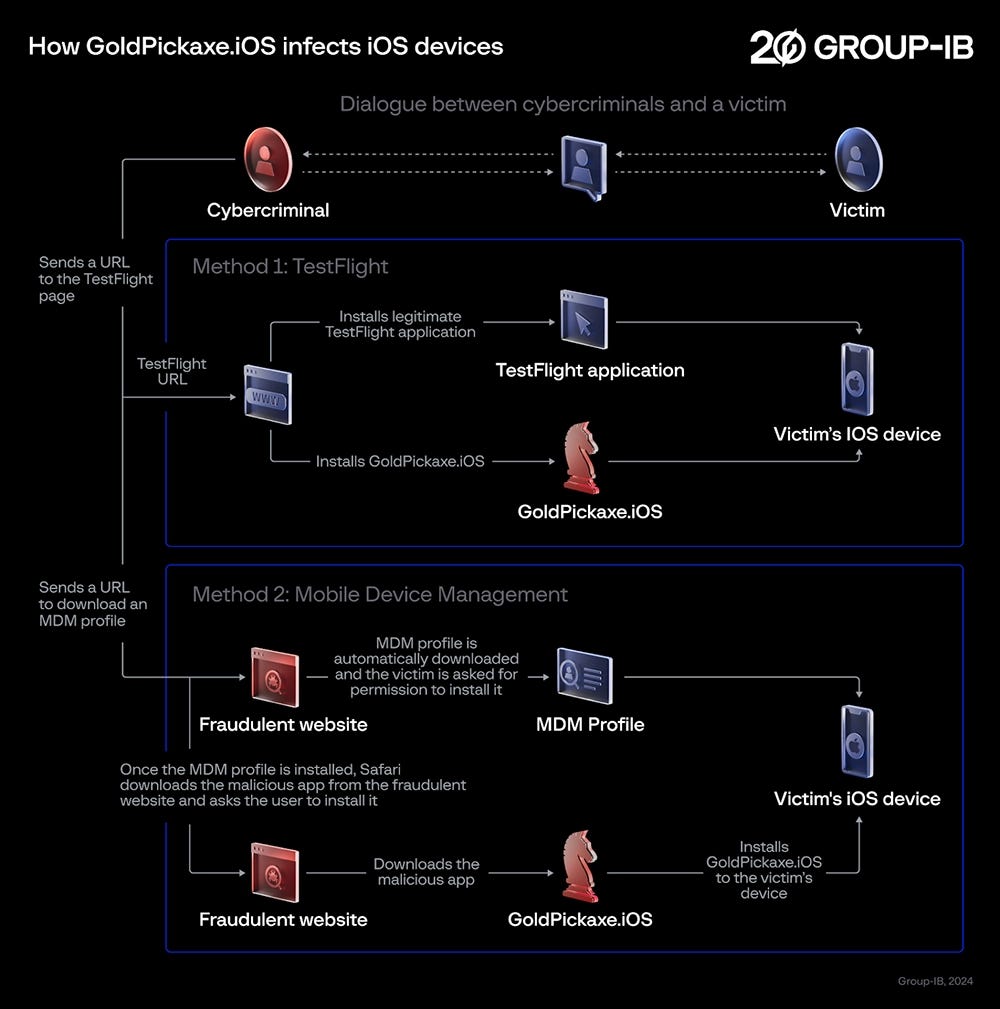
In Vietnam and Thailand, there is a new trojan attack on iOS called GoldPickaxe.
They steal biometric data and face ID from victims to compromise finance accounts. In Hanoi, a man is stolen 40,000 USD worth stock after one day. By mimicking more than 50 apps from finance institutions and government, they can have an access to your photos, SMS text messages, intercept proxying traffic and more. It’s even reported that victims receives phone call from bank representative or police impersonator asking for pictures and ID cards.
Hackers prefer to social engineering to hack a login page than a hard core coding scene seen in Hollywood movie. For GoldPickaxe, hackers exploit iOS testFlight beta testing system to install app outside the iOS mobile device management.
It is reported that the trojan don’t steal the money directly from the victim phone. But instead, it creates a deepfake and autonomously access the victim’s application. In Thailand, facial recognition has been used as an official verification for transaction and login authentication.
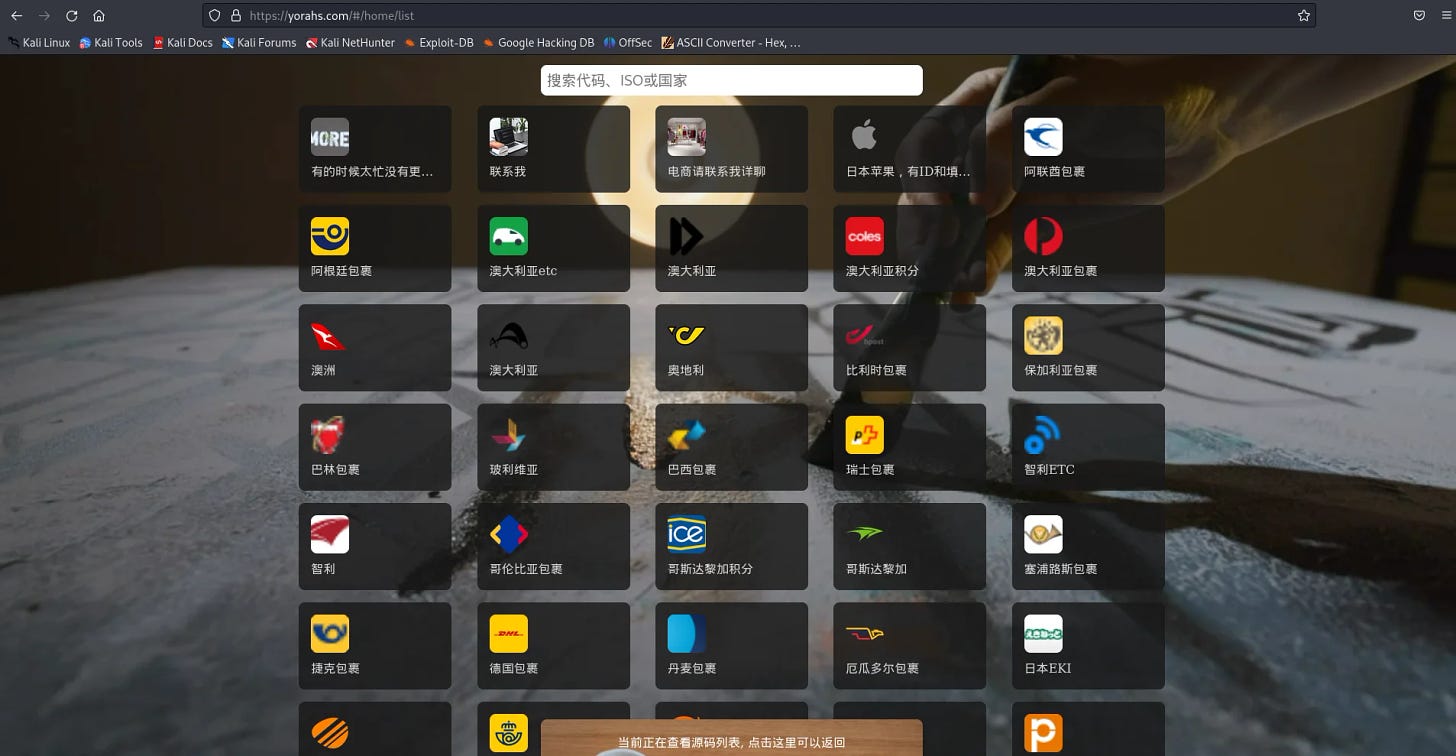
Phising-as-a-service
By targeting iMessage and Google Messages via RCS on the platform, scammers can impersonate any high profile brands and people. Ironically, it was quite similar to Telegram on reasons.
Free.
Trusted by a consumer.
End to end crypted that makes it harder to detect fraudelent and abnormal behaviour to classify content as spam or suspicious.
This is ofent known as a phising attack. Given a context of Generative AI, actors can use it to write a maleware or even exfiltrate or injecting bad data into LLMs. Using a corrupted GenAI output can expose financial institution to unimaginable both legal and damage towards customers and their own operation.
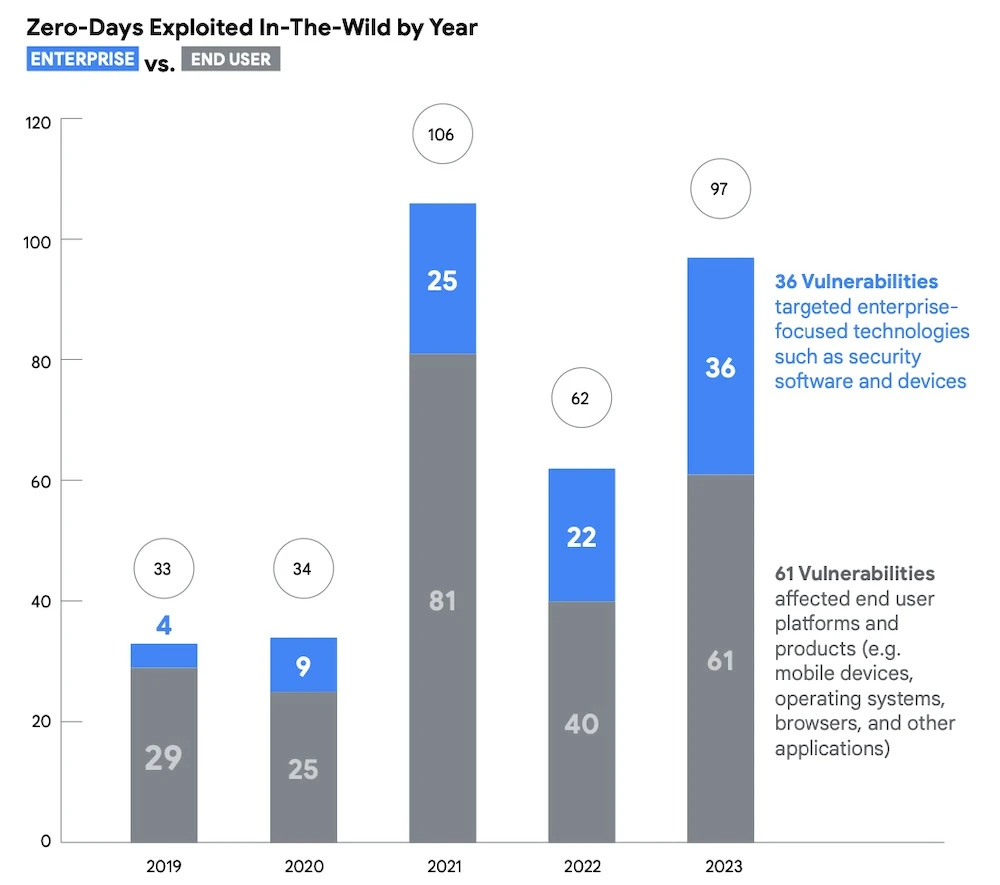
The unknown: Zero day
In the new report published a few days ago, there is a clear trend of exploitation towards consumer market, e.g. mobile devices, operating systems, browsers and applications. In the past, attackers were usually sophiscated single coders with skills, special knowledge and philosophies in developed countries.
Now hacking is a no-code commercial app easily bought in a dark web and operated by a group of paid people/ scammers, mostly from South East Asia, South America and Africa. These are places with weak law reinforcement of protecting IPs, privacy and cybersecurity and the culture that accept payment for hacked & stolen, jailbreak products, accounts and services from the West.
Reference:
https://www.helpnetsecurity.com/2024/02/15/goldpickaxe-ios-trojan/
A review of zero-day in-the-wild exploits in 2023 (blog.google)
Attackers leverage weaponized iMessages, new phishing-as-a-service platform - Help Net Security.